BIG THREE
This is where our journey begins. Get to know our business and what we do, and how we're committed to quality and great service. Join us as we grow and succeed together. We're glad you're here to be a part of our story.

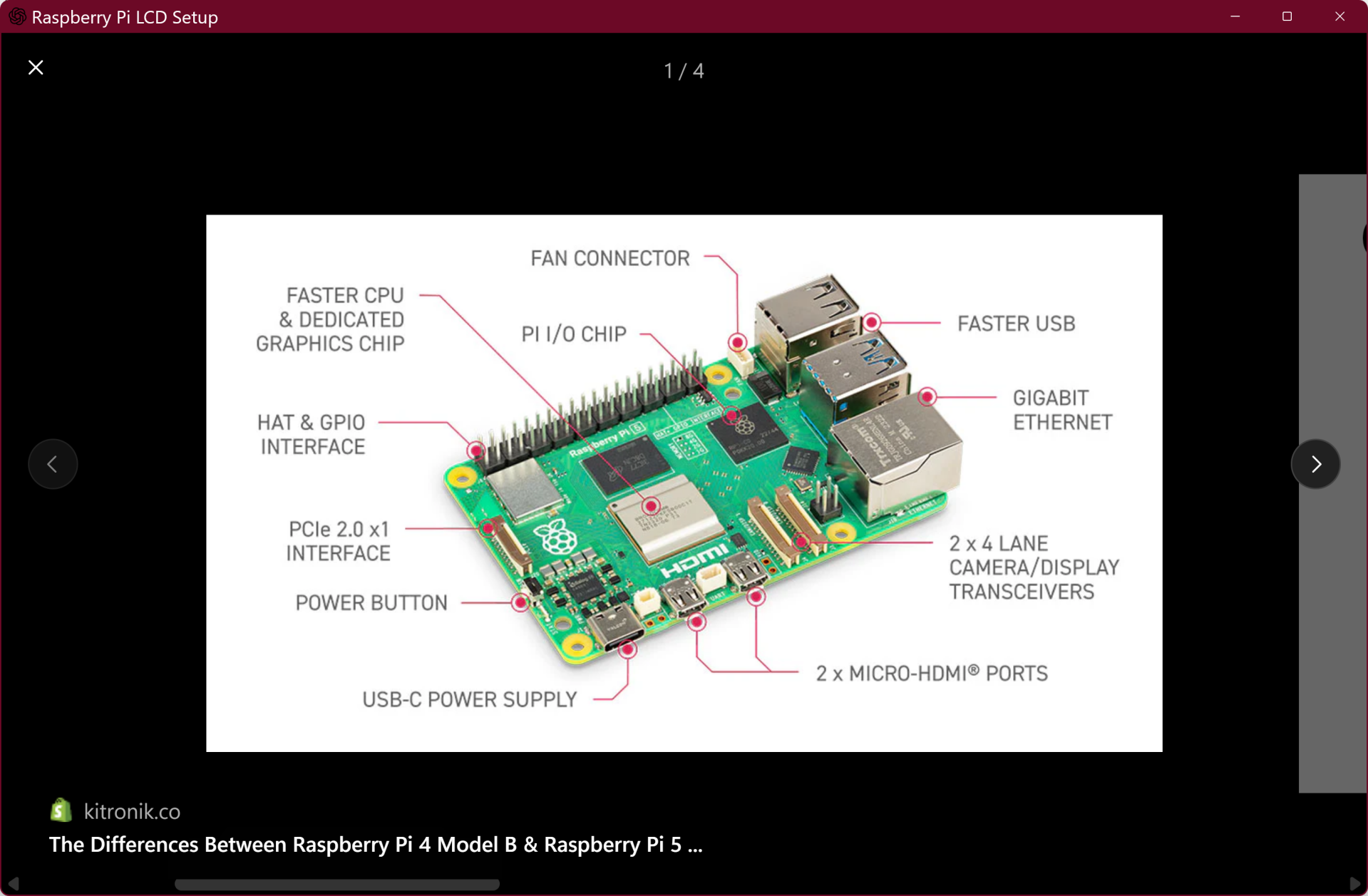
1. Unsecured Smart & IoT Devices
Most consumer smart devices:
-
Ship with default credentials
-
Lack firmware updates
-
Have open ports exposed to the internet
-
Generate unmonitored traffic
These devices become silent entry points into entire networks.
What we do
Our Focus:
-
Network segmentation
-
Secure configuration baselines
-
Traffic monitoring fundamentals
-
Router hardening & credential control
This is perimeter defense for the modern home.

2. Human Behavioral Exploitation
The majority of breaches begin with:
-
Credential compromise
-
Phishing links
-
MFA fatigue attacks
-
Weak password hygiene
This is not a “people are careless” issue.
It’s a data-pattern issue.


Our Focus
-
Phishing recognition training
-
Password architecture education
-
Multi-factor authentication enforcement
-
Behavioral risk reduction
We build awareness backed by measurable habit change.
3. Lack of Log Visibility & Data Monitoring
Many individuals and small organizations:
-
Don’t review login attempts
-
Don’t monitor router activity
-
Don’t track abnormal behavior
-
Have no event visibility
Without logs, there is no detection.
Without detection, there is only reaction.


Our Focus
-
Basic log interpretation education
-
Introduction to SIEM concepts
-
Structured threat detection thinking
-
Turning raw data into actionable insight
We teach people how to see patterns before compromise escalates.
🧠 Why These Are the Big 3
These three areas represent the device layer, the human layer, and the data visibility layer—the core surfaces where most security risks originate. Strengthening these foundations significantly reduces exposure, allowing all other security measures to build on a stable and controlled environment.

